最新下载
热门教程
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
ldap服务器用户及权限管理控制
时间:2013-11-06 编辑:简简单单 来源:一聚教程网
openldap默认的账户是cn=Manager,dc=361way,dc=com这样的一个账户 ,其写在配置文件/etc/openldap/slapd.conf文件中,但这样的一个账户就像linux下的root一样,虽然好用,不过权限太大 。出于安全考量,我们需要根据具体应用的需要,建立只读账户或者可写用户。
一、新建管理账号
新建管理账户的方法很多,可以使用像诸如 ldapadmin、phpldapadmin、LDAP browser/editor等工具,也可以通过ldapadd 或slapadd这样的客户端工具(关于两者的区别可以参看IBM 技术网)。这里假设以ldapadd为例,具体做法如下:
1、新建一 ldif文件,具体内容类似下面的:
| 代码如下 | 复制代码 |
dn: cn=bbs,dc=361way,dc=com objectClass: person objectClass: shadowAccount objectClass: top cn: bbs sn: bbs uid: bbs userPassword:: e1NTSEF9RHpONi9jM0xvaDRpd0RzN2ROVnVKZGdxYVJ0eUg1RGU= structuralObjectClass: person entryUUID: d08e9e12-a8c9-1032-9efa-9d41910b717f creatorsName: cn=Manager,dc=361way,dc=com createTimestamp: 20130903094905Z entryCSN: 20130903094905Z#000001#00#000000 modifiersName: cn=Manager,dc=361way,dc=com modifyTimestamp: 20130903094905Z |
|
2、执行如下的命令操作导入:
| 代码如下 | 复制代码 |
ldapadd -x -W -D "cn=Manager,dc=361way,dc=com" -f test.ldif |
|
注:如果条件允许,建议还是使用图形化的客户端去操作。如delphi写的LDAPadmin就非常好用。
二、给账号设置权限
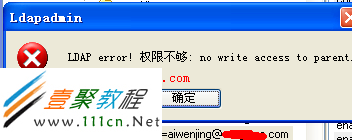
默认新建的这个账号是没有管理任何用户的权限的 ,可以用这个新建的账号登陆客户端验证。
给新建的账户赋权限也是通过修改配置文件/etc/openldap/slapd.conf来实现,具体的增加的内容如下:
| 代码如下 | 复制代码 |
| # Personal LDAP address book. access to dn.regex="cn=[^,]+,mail=([^,]+)@([^,]+),ou=Users,domainName=([^,]+),o=domains,dc=361way,dc=com$" by anonymous none by self none by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by dn.regex="mail=$1@$2,ou=Users,domainName=$3,o=domains,dc=361way,dc=com$" write by users none # Allow users to change their own passwords and mail forwarding addresses. access to attrs="userPassword,mailForwardingAddress" by anonymous auth by self write by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users none # Allow to read others public info. access to attrs="cn,sn,gn,givenName,telephoneNumber" by anonymous auth by self write by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users read # Domain attrs. access to attrs="objectclass,domainName,mtaTransport,enabledService,domainSenderBccAddress,domainRecipientBccAddress,domainBackupMX,domainMaxQuotaSize,domainMaxUserNumber" by anonymous auth by self read by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users read access to attrs="domainAdmin,domainGlobalAdmin,domainSenderBccAddress,domainRecipientBccAddress" by anonymous auth by self read by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users none # User attrs. access to attrs="employeeNumber,homeDirectory,mailMessageStore,mail,accountStatus,userSenderBccAddress,userRecipientBccAddress,mailQuota,backupMailAddress,shadowAddress" by anonymous auth by self read by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users read # # Set ACL for bbs/bbsadmin. # access to dn="cn=bbs,dc=361way,dc=com" by anonymous auth by self write by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users none access to dn="cn=bbsadmin,dc=361way,dc=com" by anonymous auth by self write by users none # # Allow users to access their own domain subtree. # Allow domain admin to modify accounts under same domain. # access to dn.regex="domainName=([^,]+),o=domains,dc=361way,dc=com$" by anonymous auth by self write by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by dn.regex="mail=[^,]+@$1,o=domainAdmins,dc=361way,dc=com$" write by dn.regex="mail=[^,]+@$1,ou=Users,domainName=$1,o=domains,dc=361way,dc=com$" read by users none # # Grant correct privileges to bbs/bbsadmin. # access to dn.subtree="o=domains,dc=361way,dc=com" by anonymous auth by self write by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by dn.regex="mail=[^,]+,ou=Users,domainName=$1,o=domains,dc=361way,dc=com$" read by users read access to dn.subtree="o=domainAdmins,dc=361way,dc=com" by anonymous auth by self write by dn.exact="cn=bbs,dc=361way,dc=com" read by dn.exact="cn=bbsadmin,dc=361way,dc=com" write by users none # # Set permission for "cn=*,dc=361way,dc=com". # access to dn.regex="cn=[^,]+,dc=361way,dc=com" by anonymous auth by self write by users none # # Set default permission. # access to * by anonymous auth by self write by users read |
|
如上面示例中就定义了两个用户,一个是只读用户cn=bbs,dc=361way,dc=com和一个可写用户cn=bbsadmin,dc=361way,dc=com 以及这两个用户对所列的字段、正则匹配的用户有相应的权限 。
更改完该配置文件后重启ldap服务,再重新登陆查看,如下
相关文章
- Ubuntu系统给用户添加sudo权限的方法 08-21
- Laravel 5.1 中的ACL用户授权及权限检查功能例子 05-14
- Swift实现HTTP网络操作库Alamofire使用详解4(用户权限认证) 12-12
- ubuntu创建新用户并增加管理员权限详解 09-29
- SAP 用户权限解剖详解 01-02
- 用户权限算法 08-10